Capstone Development Journal
Documenting the architecture, implementation, and challenges of building NestShield.
Defense Complete
February 26, 2026
Thesis Defense: Validating XAI, Gamification, and Local-First Architecture
Today marked the culmination of two years of research, development, and iteration—I successfully defended my Master's thesis on NestShield: An AI-Powered Cybersecurity Assistant for Non-Technical Users before my committee at Full Sail University.
Research Validation
The defense validated three core hypotheses through a pre-post intervention study with 42 participants (N=25 completers):
+54.2%
Ransomware Understanding
From 33.3% to 87.5% accuracy
75%
Voluntary Remediation
Gamification drove action
6.4/7
Trust Score
Local-first architecture validated
The Defense Experience
The 60-minute defense included a 10-minute live demonstration of NestShield's core features—AEGIS AI explanations, gamification mechanics, and the Threat Radar visualization. The committee posed challenging questions about research validity, technical architecture decisions, and commercialization feasibility. Each question reinforced the importance of acknowledging limitations while demonstrating confidence in the validated findings.
Key Findings
- H1 - Knowledge: XAI-driven education significantly improved security comprehension, with the largest gains in complex concepts like ransomware (33.3% → 87.5%).
- H2 - Behavior: Gamification mechanics achieved a 75% voluntary remediation rate, though a motivation-behavior gap was discovered in 2 participants who felt motivated but lacked enablement.
- H3 - Trust: Local-first architecture built exceptional user trust (6.4/7), with 93% preferring local processing over cloud alternatives. Trust increased 33% after experiencing the system.
Technical Achievements
NestShield integrated cutting-edge technologies into a cohesive educational platform:
- AEGIS with RAG: Mistral 7B LLM powered by Retrieval-Augmented Generation using ChromaDB for contextual, personalized security explanations.
- FastAPI Backend: Async architecture supporting WebSocket connections for real-time scan updates and AI streaming responses.
- React + TypeScript Frontend: Type-safe UI with gamification elements (XP, ranks, Digital Health Score) and interactive threat visualizations.
- 100% Local Processing: Zero cloud dependencies—all AI inference, scanning, and data storage happens on-device, eliminating the "privacy tax."
Retrospective
Successes
All three hypotheses validated. The convergence of XAI, gamification, and local-first architecture proved effective for security education. The 54.2% jump in ransomware understanding demonstrates that conversational AI can function as a real-time security tutor.
Research honesty paid off. Acknowledging the 40.5% attrition rate and explaining that 5 participants struggled with installation showed intellectual integrity. The committee respected the transparency.
Challenges
PyInstaller packaging issues: ChromaDB's dynamic dependencies caused RAG corruption in the standalone executable. For production, installer-based deployment or alternative packaging solutions are necessary.
Motivation-behavior gap: High gamification motivation doesn't automatically translate to action. Users need enablement (assisted remediation) alongside motivation.
Defense Materials
Note: Final thesis document includes full methodology, statistical analysis, and comprehensive literature review.
Next Steps: From Research to Product
Phase 1 (proof-of-concept) is complete. The research validates that the approach works. Now begins the 12-18 month journey to production: web-based deployment, assisted remediation implementation, scale validation with N=100+, and ultimately commercial launch targeting 200M+ non-technical Americans.
Milestone 10
February 1, 2026
Engineering Intelligence: Performance Profiling & Adaptive AI
This week, NestShield evolved from a static dashboard into a reactive, intelligent system. The goal was to implement an "Autonomous Consultant" persona—an AI that doesn't just answer questions but analyzes system telemetry to propose remediation steps proactively.
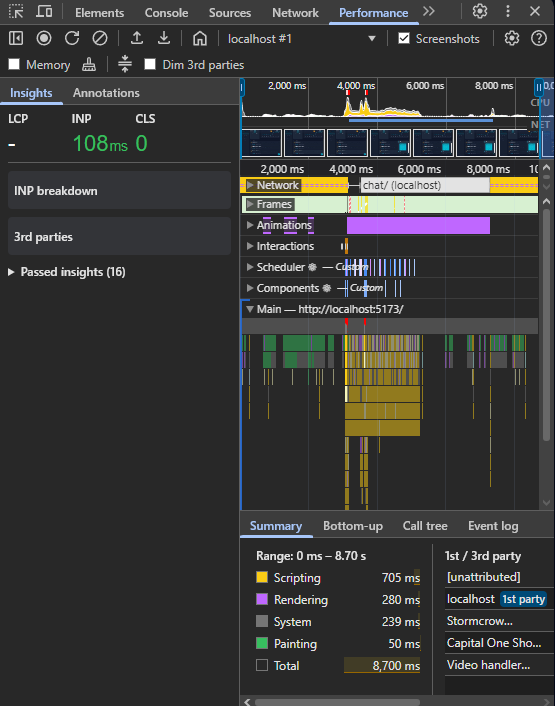
The Challenge: CPU Bottlenecks
While integrating the "Always-On" agent, I encountered a critical performance regression. The global state listener, intended to sync the Dashboard risks with the Header notifications, triggered a race condition in the React rendering cycle. This caused an infinite loop, spiking the browser's Main Thread CPU usage to 100%.
The Solution: Ref-Based Latching
To resolve this, I re-engineered the Chatbot.tsx component using a Reference Latch architecture. By utilizing useRef to track message states outside the render cycle and implementing strict dependency management in useEffect, I eliminated the redundant reconciliations.
705ms
Scripting Time (After)
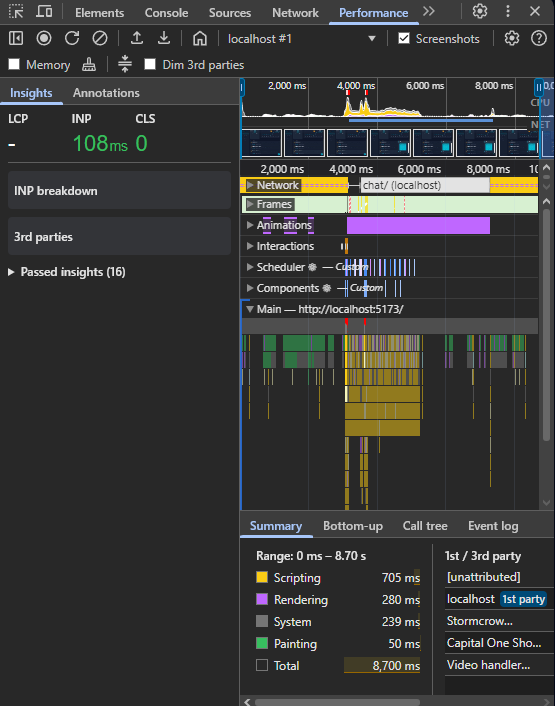
Fig 1. Chrome DevTools confirming CPU idle state after optimization.
Retrospective
Successes
The Adaptive Persona logic is working flawlessly. The system now detects the user's "Gamification Level" and switches between using simple analogies (for Rookies) and technical jargon (for Experts) dynamically.
Challenges
Synchronizing the "Notification Bell" in the header with the Dashboard's scan results required lifting state up to a global ScanContext. This refactor was time-consuming but necessary for a cohesive UX.
Next Steps
Now that the AI can propose solutions, the next logical step is Automated Remediation. I will be writing Python scripts that allow the agent to actually execute fixes (like closing ports) upon user approval.
Milestone 6
December 21, 2025
From Concept to Execution: Profiling NestShield's Knowledge Engine
This week marked a pivotal shift from architectural planning to tangible backend implementation. The focus was Knowledge Ingestion—the process of teaching AEGIS (the AI Brain) to understand complex cybersecurity standards like NIST 800-53 and OWASP Top 10.
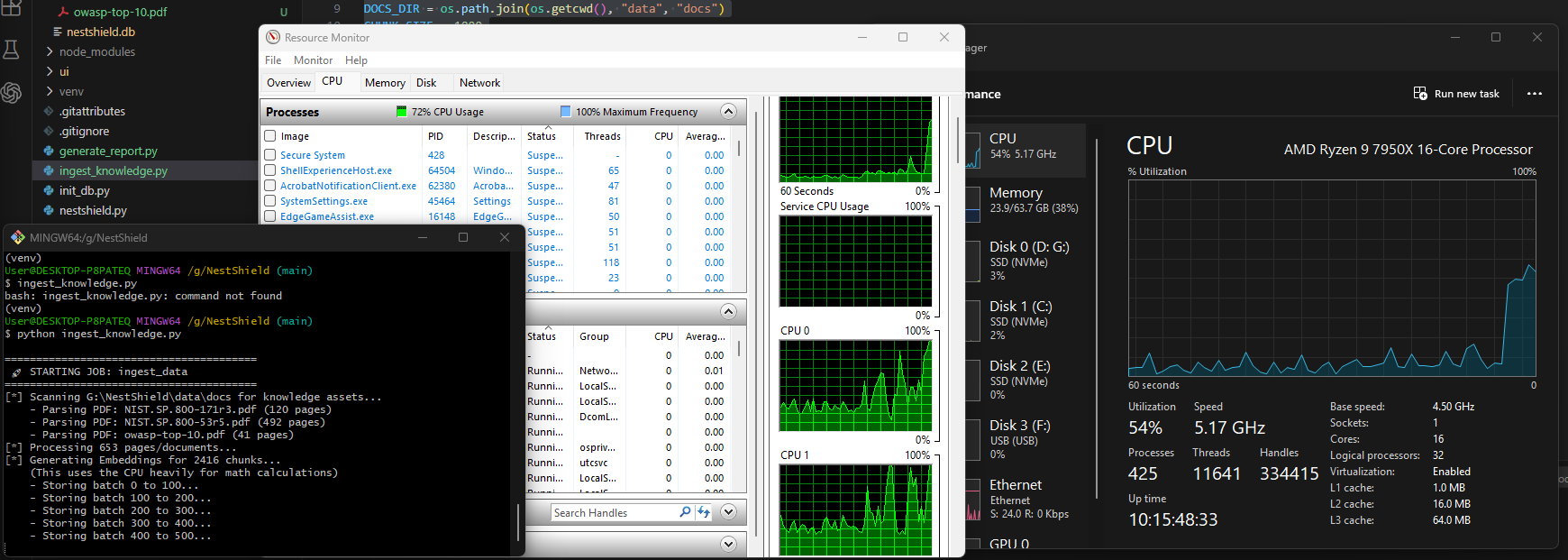
The Build
I engineered a Python-based ingestion pipeline (ingest_knowledge.py) utilizing LangChain concepts and ChromaDB for vector storage. The script performs four key actions:
- Parsing: Extracts text from dense, unstructured PDFs using
pypdf.
- Chunking: Splits text into 1000-character overlapping segments to preserve context.
- Embedding: Converts text into vector embeddings using a local Transformer model.
- Storage: Indexes vectors into a persistent database for RAG (Retrieval-Augmented Generation).
Performance Profiling Results
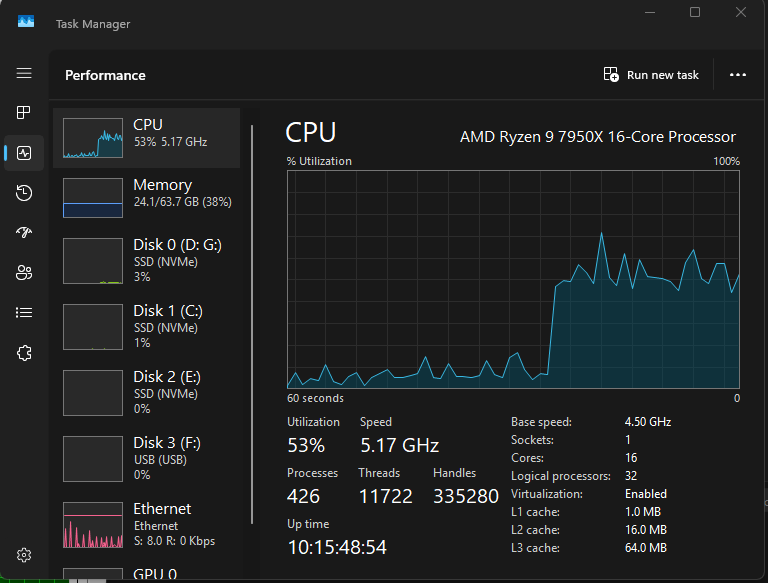
A critical requirement for this milestone was performance testing. Using psutil integration and OS-level monitoring, I stress-tested the ingestion of over 600 pages of technical documentation.
The profiling revealed that the operation is heavily Memory-Bound. The significant RAM spike (~733 MB delta) confirms that loading the Transformer model and performing matrix multiplications for embeddings is the primary resource cost. CPU usage spiked in short bursts, which is typical for vectorization tasks.
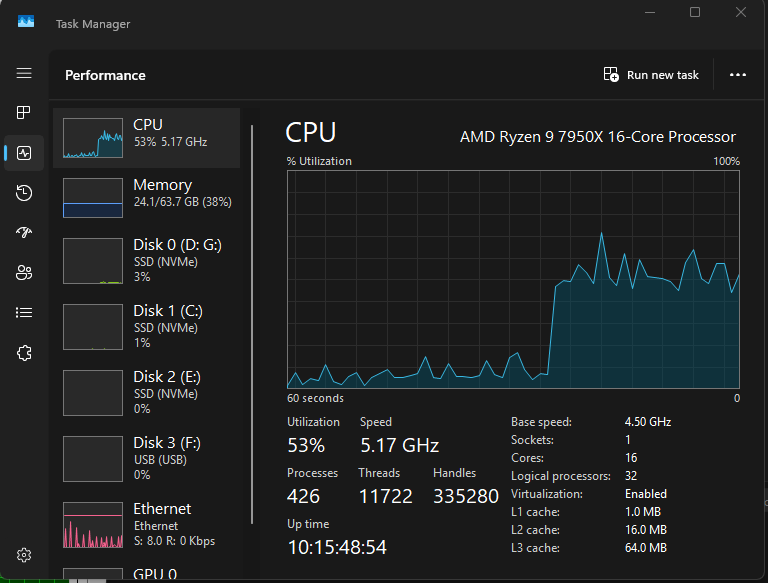
Fig 1. OS-Level CPU Activity
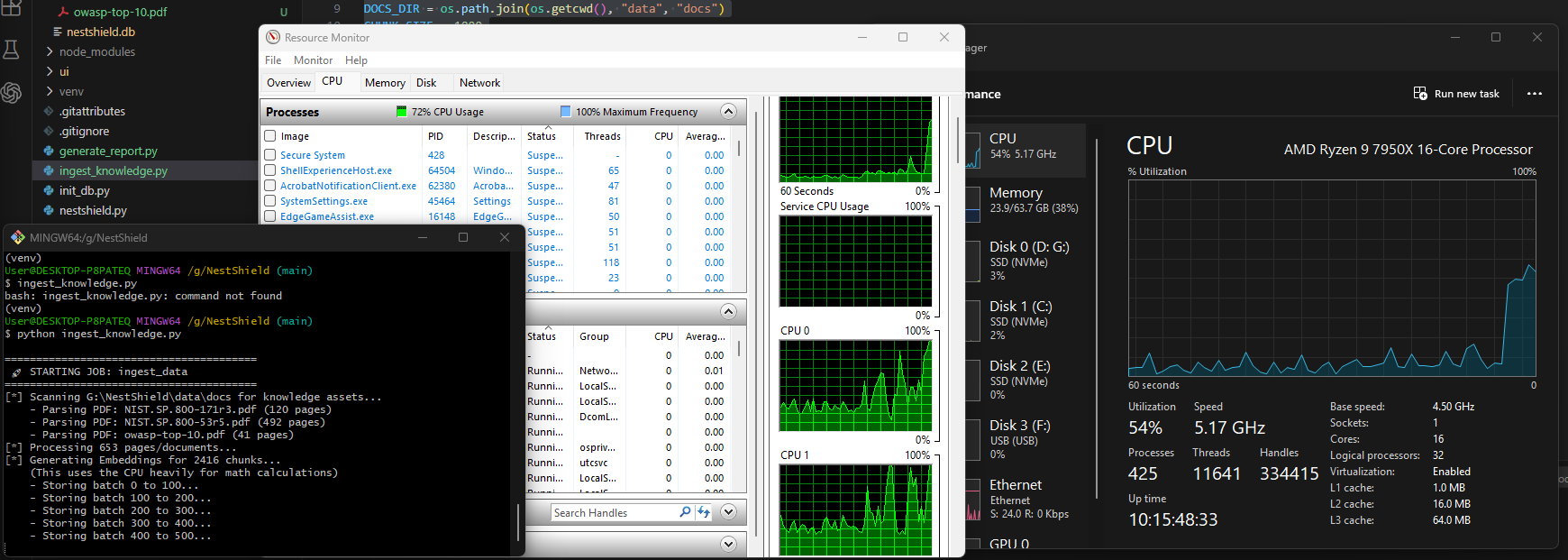
Fig 2. Script Performance Output
Retrospective
Successes
The error handling architecture proved robust. During testing, a corrupt ISO-27001 PDF failed to parse, but the script caught the exception, logged it, and continued processing the NIST and OWASP documents without crashing. This "fail-safe" design is crucial for production environments.
Challenges
Accurate CPU profiling within Python proved difficult. The library `psutil` often reported 0.0% CPU usage because the sampling interval missed the rapid micro-bursts of the vector calculations. Moving to OS-level monitoring (Resource Monitor) was necessary to get the full picture.
Next Steps
With the "Brain" now active, the next phase is connecting the React Frontend to this knowledge base, allowing users to ask natural language questions about the documents I just ingested.
Milestone 1-5
November 23, 2025
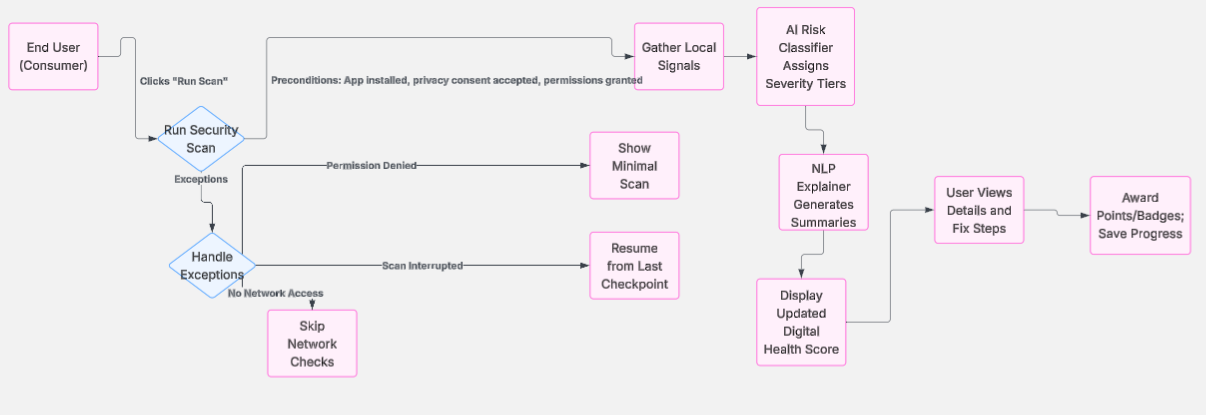
Laying the Foundation: Research & Architecture
The path to building robust software begins long before the first line of code is written. This month, in the Research, Planning, and Design phase of my Master's Capstone, I focused on transforming NestShield from a concept into a tangible architectural plan.
Features & Architecture
My primary goal this month was to design the collaborative intelligence framework. I utilized Python for the backend logic planning and created high-level diagrams to map out the user flow. The biggest challenge was determining how to handle data privacy within a collaborative environment.
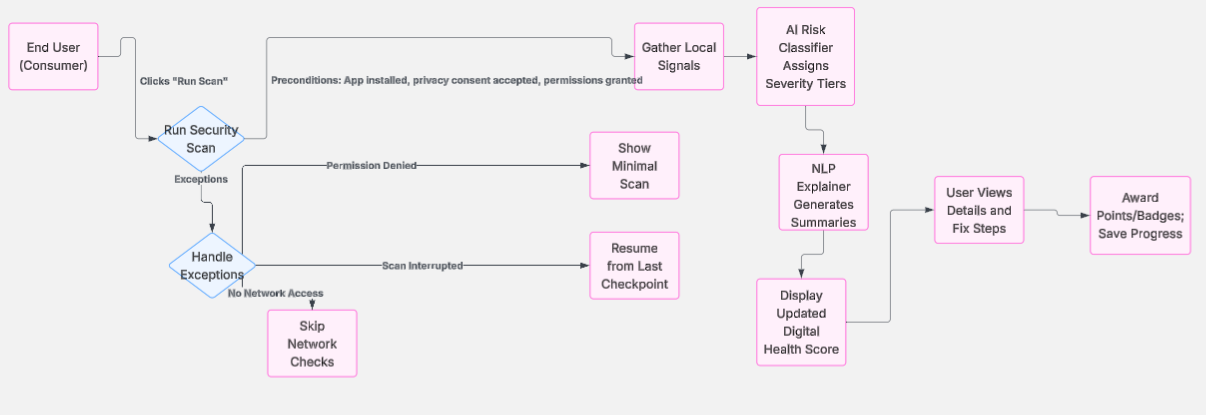
Fig 3. Initial Architecture Flow
Retrospective
What went right?
I successfully defined the core "problem statement" for NestShield. By attending the "EstiMate" defense presentation, I learned the critical importance of scoping. I narrowed my focus specifically to the collaborative intelligence aspect.
What went wrong?
Time management was a hurdle. Balancing technical research on Python libraries with the academic requirements of the proposal paper led to some late nights.